Rudimentary Cryptology: Substitution Ciphers
TLDR: A walkthrough of historical cipher attacks and defences.
Table of Contents
Talking in Code
Okay, we've done a lot of talking about theory and background, but the best way to learn cryptology is to get your hands dirty making and breaking systems. These systems are all historical, generally linguistic and alphabetic ciphers that have some serious flaws. It should go without saying that they will not keep you secure and you shouldn't use them to hide anything you care about, if you get caught committing crimes using one of these algorithms and blame me, rest assured I will happily show up to the court hearing to tell the jury how much of a complete moron you obviously are. These systems almost all predate Kerckhoffs and so they are exactly the type of algorithms he intended to put an end to. Here we will build up knowledge of how cryptosystems are made, even give it a go in code if you like, then we will talk about where their flaws are and look at ways to tear them apart. To prove how weak they are I would point out that this sort of attack only really works on the algorithms in this first few articles of the series, I have to actually build the more modern ones badly to stand a chance of breaking the cryptosystem, that's how strong modern cryptosystems are.
Hiding Secrets from the Kids
Anyone who has kids or a dog will know there are certain words or phrases you should probably avoid mentioning around them. It might be a favorite snack or hobby, a visitor or location, perhaps surprises, or even just a trigger word and you could do without the headache that follows. It's a really normal thing and usually not nefarious in the slightest, we all need to keep secrets from time to time purely for our own sanity. As adults and even young adults, we tend to pick up a few clever ways of doing this, we might start by spelling the word knowing they can't spell yet, or write it down since they can't read - you should thank your lucky stars you never had to deal with hyperlexia by the way. It all tends to revolve around things the kids don't know how to do yet, and yes its obscurity, but you don't need RSA to avoid ruining Christmas. As they get older and smarter our techniques have to advance else our code would be cracked, and a lot of these little clever games we play have value to teach us about linguistics and cryptography.
Pig Latin
If you know your history you probably know the Romans spoke Latin, and you might even know it evolved over time meaning it is split into 7 different categories, Archaic, Classical, Vulgar, Late, Medieval, Renaissance, and Ecclesiastical. You might even be forgiven for thinking Pig Latin refers to Vulgar, but no it isn't really Latin at all. We discussed before how different languages can be used hide information, and that's where the idea behind Pig Latin comes from. Pig Latin is actually a mockery of how Latin sounds, by aiming to move vowels to the front and using predictable suffixes it mimics how Latin sounds to the untrained ear, you've probably heard it spoken but didn't necessarily know what it is. Pig Latin is where you take English words and break them up to distort them, so to use the Monsters Inc. phrase "Look in the bag" becomes "Ook-lay in the ag-bay" which sounds like gibberish. Its rules are actually more complex than they appear too, here they are:
Consonant Rule: If a word starts with a consonant or consonant cluster (like "ch," "th," or "gr"), move all letters before the first vowel to the end of the word, then add "ay". Examples: "dog" -> "ogday"; "trash" -> "ashtray"; "glove" -> "oveglay".
Vowel Rule: If a word begins with a vowel sound (a, e, i, o, u), simply add "way," "yay," or sometimes just "ay" to the end. Examples: "eat" -> "eatway" or "eatyay"; "apple" -> "appleway".
Alternative Rule (Vowel): Some variations simply add "yay" to the end of words starting with a vowel, such as "out" becoming "outyay".
Word Transformation Examples:
- Hello -> Ellohay
- Pig Latin -> Igpay Atinlay
- Child -> Ildchay
- Eat -> Eatyay
Have a play around with it, see if you can build a program to encrypt and decrypt, you will find its a lot more tricky than it appears. It is however a mostly verbal trick rarely seen written down and even less so on computers, but it does make a good example of how we can quickly alter the language to hide secrets. Of course as this cipher is a simple mechanical method with no secrets, it is trivial to compute and the easiest way to attack it is simply to understand the method and decrypt it. So the first rule of cryptography, there needs to be a secret or there is no security and anyone can decode it simply by knowing the rules.
Codes vs Ciphers
So the words "code" and "cipher" have cropped up a lot so far and they seem to be used interchangeably with little regard for the text and no definition required. Both these words are fairly common in English parlance and don't really need explanation, but have you ever stopped to think what they mean or how they differ? There's a pretty good example in the last paragraph, but allow me to elaborate a little. When you hear of a spy like James Bond speaking in code or using codewords, you immediately know they mean he's using substitution to confuse the enemy and obscure secrets from them, this is the truest meaning of the word. You can get an idea for how this works with the phrase "The pig is in the poke" from the Simpsons, in this instance Marge is the "pig" and the "poke" is presumably their house or kitchen, Marge confirms this by then telling Homer she does not care for that codename, a reasonable assertion given how unflattering it is, but after all Homer is simply trying to keep her safe. Check out this map of UK postal codes for a more mundane example:

Postcodes are an excellent example of a practical everyday "code" it provides a simple, short, easy to remember code like SW1 and that information can be substituted when needed for London, South West, more specifically the area of Downing Street and Buckingham Palace where the heads of state live. So what's a cipher? Ciphers are like codes, but they are devoid of meaning, often deliberately so. The point in a cipher is make a mechanical change that is predictable and reversible, but makes the result uninteresting and appearing to be completely random, we will discuss more about why later. So a "cipher" is more like what we did with Pig Latin, because the entire purpose is to make the words nonsensical to evade detection.
Historical Ciphers
Most historical ciphers are based around linguistics, it makes a lot of sense, most of the time you want to encode messages, which as the name implies are usually based around some sort of language. This has a lot of problems as we will see and discuss later, but as a starting point its not a bad one. To my knowledge Pig Latin is actually much newer than most of these ciphers, but it seems likely the users of these ancient ciphers probably played around with similar ideas, firstly its a very human behavior to play with language and patterns, especially as kids, but secondly these ancient ciphers very quickly begin to learn from the mistakes of these simplistic substitutions.
Monoalphabetic Ciphers
The first thing they learned is that trying to distort whole words is problematic, a word has a lot of complexity and meaning built in, its length and characters can be quite variable, and there are a lot of them well over 10,000 in the English language. This is important because you need to map your input to an output in a 1:1 ratio, the ciphertext must only relate to one plaintext, so if "dog" becomes "cat", "potato" cannot also become "cat". The reason for this is simple, encrypting is easy, both become "cat", but when you try to decrypt you have a problem, is "cat", "dog" or "potato"? There's no way to know, the information has been lost, as it happens you can map a single plaintext to multiple ciphertexts, so long as they are not shared with anything else. This is something that will come back a bit later, but as for right now its really a waste of time, because all that really does is increase the number of ciphertext values, which for words is already a problem.
To reduce the number of values for transcription and make it easier to calculate, rather than change entire words most ciphers instead chose to change each letter. This had a few benefits beyond simplicity and providing only 26 characters to calculate, most notably it tended to make it easier to alter the word more completely, so you couldn't tell from a glance what the word was even when encrypted like you often can with Pig Latin. This simple idea gave rise to what we call the Monoalphabetic Ciphers, because they change the letters of the alphabet in a singular way.
Caesar
Yes, that Caesar. This method has been attributed to the famous Julius Caesar, but we have no contemporary accounts of him ever using any encryption methods, but maybe he was just that good. We know there are far older attempts at encryption, but our understanding of them is poor, so this is one of the first we properly understand, and it is also the simplest of the monoalphabetic ciphers, which is probably why it survived. What we do know is Caesar was a brilliant military general and a master statesman, he could undoubtedly have benefitted from having an encryption algorithm when the rest of the world didn't. Despite its simplicity Caesar lived in a time when few could read and write, and enemies rarely shared a language meaning even a simplistic cipher like this one could actually have been all that was needed.
So how does it work? Well lets start with the letter "A" and I'll show you, Caesar is a shift cipher, this means that you simply shift the letters by a given amount. Start by writing out all the letters A to Z in a line, then next to it do the same again and cut the paper between the two, now you can move one list relative to the other. With a shift of 1 "A" becomes "B", "B" becomes "C" and so on all the way up to "Y" becomes "Z" and "Z" cycles back around to "A", it actually becomes a little easier to track if you put all the letters on a rotary dial like below, which is what gives this shift cipher its more modern name of ROT, short for rotation.

Supposedly Caesar used the standard shift of 3 meaning A -> D, and thus "the quick brown fox jumped over the lazy dog" becomes "wkh txlfn eurzq ira mxpshg ryhu wkh odcb grj" although it is standard practice to use all capitals and remove spaces to remove information that might give away the cipher. However you can use any shift between 0 and 25 inclusive with this method, by using the shift this way you introduce something else the Pig Latin cipher didn't have, a key, meaning we now have a piece of information required to decrypt, so we have taken a significant step towards a more secure algorithm by introducing a secret that must be passed beforehand. There are two commonly occurring variants of this cipher that its worth knowing about firstly is one known as ROT13, this is basically just a typical Caesar with a shift of 13, 13 being half of 26 making ROT13 a full inversion that is very confusing for the human eye if you don't know what you're looking at. The other variant is ROT47 which is bizarre at first glance since the cycle just repeats after 26 but ROT47 adds more characters into the mix up to a total of 94 to make it more tricky to solve meaning 47 is a valid rotation analogous to ROT13. Decryption in case you haven't figured it out yet is simply a case of a reverse shift that is just as easy to do as the encryption but in the other direction meaning this key is symmetric, something that we will explain later.
Affine
I'm really sorry to those who hate maths, but here is the point when we must finally embrace it, as it is difficult to understand the Affine cipher without it, I will try to take it slow. Firstly I'd like to point out the Affine cipher isn't actually that old, being created in 1983, but it is cryptographically interesting, we can use it to show how to expand the keyspace of Caesar without a great deal of complexity. The reason you'd want to do that will become apparent in the brute forcing section, but for now lets look at how its done. So Caesar can have 26 possible keys, one for each letter of the alphabet, ROT47 extends this to 94 but they both use the same approach, a single flat line or rather a cycle and you simply add or subtract the key to calculate the position of the character you need, so \(y = x + a\) where \(x\) is the plaintext and \(y\) is the ciphertext, leaving \(a\) as the key. The Affine key looks more like this a=5, b=7 having two parts, and is applied like this \(y = ax + b\) so the first part is a multiple of \(x\) (the plaintext) and then \(b\) is added to it like before, doesn't sound that interesting.
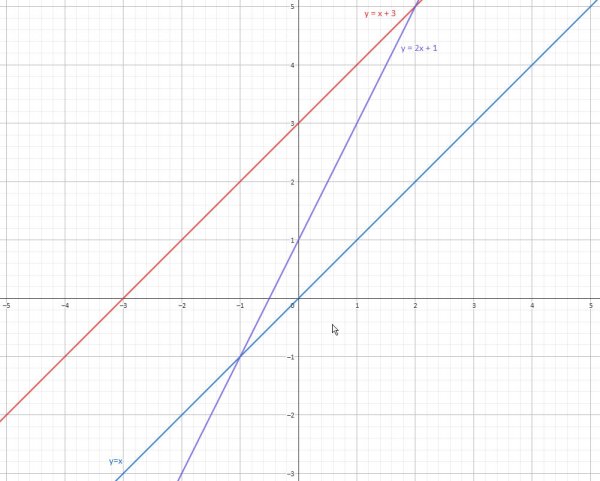
The big difference though is that multiplication helps to scatter the plaintext making it harder to detect, and how this plays out is easiest to see if you change \(a\) to \(m\) and \(b\) to \(c\) giving \(y = mx + c\) which is the basic linear equation graph. If you look at the graphs you will see how the graph (just put the equation into Wolfram Alpha) for Caesar \(y = x + c\) just transposes the line \(y = x\) up and down the y-axis depending on the value of \(c\) and that difference is all that distorts the plaintext which is why its so easy to read and undo. The \(m\) in Affine however actually alters the gradient of the line, so even if you happen to pick exactly the right value for \(c\), only that one value will be correct and you will have no idea which it is as the text will still look like complete gibberish.
This simple addition of a second part fundamentally alters the shape of the keyspace and increases it significantly. Its quite involved and beyond this stage of understanding by some margin, involving \(a\) being coprime and using Euler's Totient function, but if that interests you do look into it as it will help improve your cryptographic knowledge, otherwise you'll just have to trust me. The keyspace for Affine using 26 characters increases to 312, and for 94 characters to 4,324, this simultaneously makes it a lot better than Caesar, but also still completely terrible, we will look into why this is in a bit. If you're like me you're probably wondering if this concept can be expanded to quadratics and beyond, the answer is yes it can, and the results get interesting as the ciphertext no longer has a linear relationship to the plaintext so it begins to become less predictable. The problem is though, just as how the Affine required \(a\) to be coprime, the higher order you go the more limitations creep in, and it remains a monoalphabetic cipher so is still vulnerable to all the usual attacks despite the keyspace growing significantly.
Atbash
The Atbash cipher originates in Hebrew interestingly, though maths is universal so that doesn't matter much. This one is pretty simple really, write out the alphabet, then write it out in reverse below and map between them to transcribe, a to z, b to y, c to x etc. It seems logical that you could apply a shift to this with no additional problems though there's no indication that anything more complex was used. This cipher recognizes the problem with Caesar that the order of letters is kept the same and so it will never stray too far from obvious, by reversing the order it provides a solution that is a bit less obvious but doesn't really tackle the larger problems, a textbook example of obscurity being used to try cover a hole in security and having minimal effect.
Mixed Alphabet
A mixed alphabet cipher isn't exactly a specific cipher as such but is more a property displayed by many ciphers and a useful way of establishing an important idea in cryptography on a larger scale. It effectively is a way to perfect what Atbash was trying to do by finding various ways to randomize the order of the alphabet and remove any predictability from it. It's a small change in terms of security, but in its defence I've seen this simple trick trip up a lot of professionals, because rather than running an automated attack, you need to understand how the attack is run to spot and correct errors. This is a level of understanding surprisingly few actually have today as even those that learn cryptographic techniques rarely learn how to build an attack, they are far more likely to rely on existing and known ones, with good reason I might add. It's worth noting this oddity though as it shows just how small this particular niche is, and that is important information for someone hoping to make money from cryptographic systems. But enough about career prospects, lets consider how to visualize..
So we talked about how with Caesar and Atbash you can write them out in a linear way, and we saw with Caesar how you can use 2 concentric circles to do the same thing and it makes more sense as there is no beginning or end it simply cycles around. Let's think of that inner circle like a pizza because it makes describing the changes easier. To build a device to do the same for Atbash we need take all the slices of that pizza out and put them back in the reverse order, hardly rocket science. To do the same for Mixed Alphabet we need to put the slices back randomly, so any sense of order is completely lost, the idea being that the loss of order makes it impossible to predict what the key is since the key in a system like this is simply the list of letters in the correct order to match a-z. Unfortunately this does nothing to prevent the attacks monoalphabetic ciphers are weak to, it just makes the attackers job a little more confusing. It can be difficult to grasp at this visualization though as without a clear order the mappings can get quite messy and its better to recognise that there is no longer much of a cycle to speak of since without order the pizza has no real meaning. So instead I like to think of this cipher like a plugboard, a collection of circuits for each letter that you can map to be swapped with any other simply by attaching a wire, and this is a vital component used in some later ciphers.

Okay we've looked at what it attempts to do and how to think about it, but not yet how to implement. Caesar is pretty obvious, and Atbash ostensibly the same, and the transcription process here is the same, but there remains the lingering question of how to generate a random list of characters, especially in antiquity before they had computers to do it for them. They had a really simple method for this, and in a way its quite brilliant though not that random. Instead of passing the entire list as a key which is hard to remember, they would use a keyword and pass that to their recipient, so lets use "cinnamon bun", its easy to remember. So first up we need to make this key ready, we remove all spaces and any duplicate characters, leaving us with "cinamobu" which is decidedly more cryptic but its important we don't duplicate letters for the reasons stated previously about many to one transcriptions. Then we simply go through the alphabet skipping any duplicate letters to build what some call a deranged alphabet giving us "cinamobudefghjklpqrstvwxyz, as you can see, not very random but much more chaotic than Atbash, and easy to replicate.
Bacon
The Bacon cipher, designed by Sir Francis Bacon, is not really a monoalphabetic cipher, in fact the remaining ones in this section aren't either. Officially because of how it's used, it's actually a form of early binary encoding and steganography, but the cipher itself like the others here is a substitution cipher, and in that sense it is not greatly different from the monoalphabetic ciphers. Let's pick apart these terms and learn what they mean so we can understand it a bit better. So how does the Bacon cipher work? Well first of all, its a substitution, we switch each letter out for a number between 0 and 31, why 31? Because its a power of two as the numbering system we will use is binary so the number of powers of two you have is how many bits there are in the number, in this case 5 (which is a little unorthodox but its an old system), a bit like how we know how big a decimal number is by counting the places. So why to the power 5? Simple, because Sir Francis Bacon was English, there are 26 characters in the English alphabet and 5 bits is the minimum required to display 26 distinct numbers, the final 6 just aren't really used.
So if its a substitution and we start with A = 0 and count up, B = 1, C = 2 etc up to Z = 25. We can then binary encode these numbers into 5 bits, so A = 0 = 00000, B = 1 = 00001, C = 2 = 00010, Z = 11001. What you will ordinarily see if you use something like CyberChef is that instead of 1 and 0 they use a and b, this is because before computers binary hadn't been established like we know it, and instead Bacon used letters as placeholders not really recognising this as a numbering system. So A = aaaaa, B = aaaab, C = aaaba, Z = bbaab. This is not actually complete though, the cipher was purely an encoding method. Here's the bit that often gets lost in the modern world and it actually makes the Bacon cipher quite clever, to encode a secret message a regular message would be sent, and then within that text each letter or words would be subtly altered. Here is an example "It always rains on Tuesdays, how frightfully inconvenient." Did you see it? Its quite subtle, let me show you how to decipher it, it's all in the italics.
First lets remove all the spaces and punctuation: ItalwaysrainsonTuesdayshowfrightfullyinconvenient
Next we'll organise them into groups of 5 which makes it easier to see: Italw aysra inson Tuesd aysho wfrig htful lyinc onven ient
Then if its normal we'll replace with an a, and if its italic we'll replace with a b: aaaba aaaaa baaba baaab baaaa baabb ababa aabaa aaaaa aaaa
Then we can decode that and we get: catsrulea
Clearly the end is just padding to make it fit easier and the message is "Cats rule". So this cipher is very much reading between the lines when used properly, but this hiding of the message within data in plain sight, that's why this cipher is steganography. Steganography itself is really just a very advanced form of obscurity, proving yet again that despite its blatant flaws as a concept, for providing security from most people simply hiding it out of plain sight is enough most of the time, it just will not hold up against a genuinely determined or skilled individual.
Pigpen
We've had Pig Latin, and Bacon cipher, now to the Pigpen cipher, I'm sensing a theme... especially amusing since I have a language project named PorkBrainz because it implements Hamming Codes, a whole different kind of code that deserves its own series to discuss, a job for another day. Pigpen as ciphers go is fascinating to look at, but not actually very interesting under the hood, it forms a group of ciphers including the Templar cipher and others that are often refered to as Masonic ciphers, implying that these were how secret societies hid their messages. There is a little truth in that but as you'll quickly see these ciphers are all very similar, and generally all flash and no trousers. Here's a quick Pigpen example:

Looks super cryptic doesn't it? Well in reality its just an image based system of substitution, all you have to do is figure out which letter each image belongs to and poof you're done. I've delved deep into secret societies, alt culture and the occult and found many like this, and their biggest failing is these pseudo-languages all need a frame of reference and that is their weakness. Building a full new language is hard, like a lifetime's work hard, so they never do that, instead they just invent a set of symbols that map back to the alphabet, so all you need is a reference for that system. Take a look at the one for pigpen below:
Clever, but doesn't take a genius to figure out, and once you have that the entire language opens up like a book. The biggest problem is that this is just another case of obscurity really and relies on the weirdness to confuse people, and because that's its only defence, it crumbles under a frequency analyzer just as easily as Caesar does. As I say all the other ciphers like this succumb to the same problem so it doesn't matter what fancy images you use, even the magician's alphabet if you like (yes, there is one, I've written manuscripts in it before) the images can easily be pulled back to their native language, literally speaking French is a better defence.
Nomenclator
The Nomenclator is a late medieval cipher that persisted for quite some time and produced some ciphertexts that even today give the historians a lot of trouble. Pinning down exactly what it is though is quite difficult, because in truth it is more of a group of ideas about cryptography that differed greatly depending on who exactly you were talking to. Due to this getting actual information on how they worked is quite hard, not least because there is no single method and in fact there is no singular consistent across the board practice in how it was done. In fact the biggest trouble with the Nomenclator is that it simply isn't obviously distinct from any of the other types of substitution cipher, it is both all of them and none of them at once, which makes it very tricky to place. So what do we know, well for a start we can get some ideas from the name "Nomen" is latin for "name" which makes sense since names of things, places and people are typically substituted for numbers or symbols like a shorthand key system. The exact names and numbers involved depend on the context, these ciphers were often used by officials recording events meaning the emphasis was more on recording things quickly and accurately rather than secrecy. This is also backed up by the name since it didn't always mean a cipher, in Ancient Rome, a nomenclator was a slave whose primary duty was to accompany their master—often a politician—in public to whisper the names, professions, and important details of people they encountered, the cipher was effectively a notation sheet such a person would carry with them.
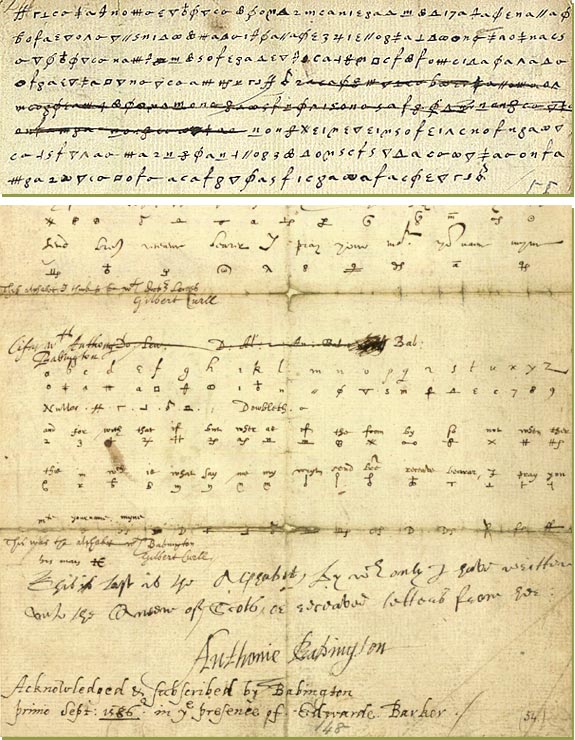
The true strength of the Nomenclator though was what we would now call defence in depth. In addition to this number/symbol based keyword dictionary substitution, something more akin to a codebook than a cipher, a more traditional substitution cipher was then applied to the text. Something worth noting is this sort of double encryption usually results in producing garbage data, effectively it destroys too much of the original data and can render it unrecoverable, the usage of numbers and symbols as keywords was quite deliberate as they are unaffected by any of these simple ciphers. This simple trick means that nowhere is double encryption actually occuring, but you do have two separate encryption methods in play, ensuring that anyone reading this who isn't the scribe it was written for won't see the complex web of intrigue just a mass of nonsense. The reason they did it this way is not because they didn't have better options, they had access to polyalphabetic ciphers, but they tended to be complex, whereas this method produced text that a scribe could translate on the fly simply by having knowledge of their regional codebook and simple ciphers. This is why the Nomenclator persisted for so long, it was a very practical algorithm, that met the needs of an intellectual niche.
Book Cipher
The Book cipher is again an esoteric sort of substitution cipher, and as the name suggests involves a book, ideally it should be a well known book of which there is a standardized copy and that it is reasonably likely both sender and recipient has easy access to. The idea here is that the well known book serves as a sort of codebook, in the simplest form the sender sends a list of numbers, each number is the position of the intended word in the book. To save me counting words which is a laborious and error-prone task allow me to steal an example or two from Wikipedia, the list "335 219 881, 5600 853 9315" when using H.G. Wells' The War of the Worlds would produce "all plans failed, coming back tomorrow" since the 335th word of the novel is "all", the 219th is "plans", etc.
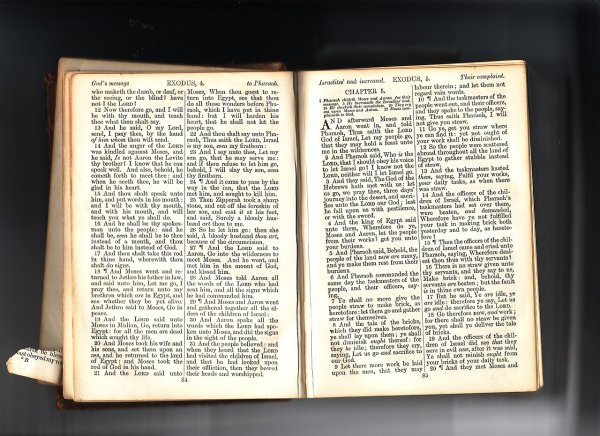
A slightly more clandestine method was to only use the first letter of each word, so using the same book "12 10 / 50 31 59 34" would produce "nineteenth", "of", "almost", "mortal", "might", and "own" or "no ammo". As you can see though this limits how quickly you can send information so while it adds a layer of obscurity, it loses a lot in the process. Another method designed to remove the difficulties in counting words was to supply triplets for page, line, position, this was quite common with the King James Bible, one of the most widely printed books of its time. As you can see this method isn't terribly technical, and thus despite its labourious nature it persisted a long time in different forms. It tended to gravitate towards built for purpose codebooks to make the work easier and as a concept it was still technically in use in the German codebooks used alongside Enigma in World War II.
Brute Forcing
So how exactly do you kick the front doors in of a cryptic letter? Well sadly its not remotely that fun, the name is largely metaphorical. Let's take the Caesar cipher, here's something for us to work on:
"L kdyh qrwklqj wr riihu exw eorrg, wrlo, whduv dqg vzhdw."
When you look at that there's nothing that immediately gives away how to solve it, once you get used to it you can quickly spot its likely a monoalphabetic cipher, but that doesn't really move us on that much. The trick to brute forcing this is to look at the size of the keyspace, there are 26 potential keys, which is pretty low. If you wanted to you could probably write them all out by hand, but why bother? A modern computer can handle over 4 billion instructions per second, which assuming to write each letter of the alphabet takes an instruction a key table would take 52 instructions, then with 44 characters in the ciphertext you can probably check each potential key within 100 instructions. A quick bit of maths and that means you can check 40 million potential keys every second, meaning Caesar's humble 26 is child's play, so just brute force it by calculating every permutation.
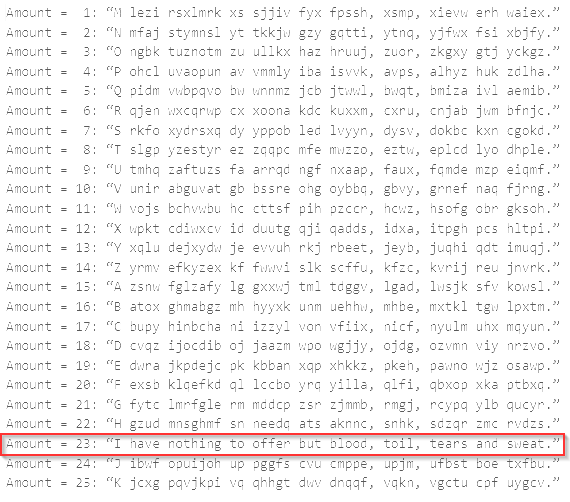
Would you look at that, all the keys run in a fraction of a second and oh looky there, one of these things is not like the others. This is what it means to brute force, simply try every available option, it isn't universally true but generally all of the ciphers mentioned tend to be weak to this sort of attack. The reason why is generally the limited size of potential keys, if you can make it large enough you can make it difficult, but with such speed at our fingertips it becomes very difficult to raise the keyspace high enough for any of these ciphers to last any sensible amount of time. This is where polyalphabetic ciphers come in, which will learn about next time. Let me leave you with something, this is a piece of code I keep in my cryptolocker, take a good look and you'll see it's for brute forcing, play about with it, build your own, learn from it.
#!/usr/bin/env python3
# rotsploit.py - A simple python script to exploit the small keyspace of shift ciphers.
# Usage: python3 rotsploit.py -f <file> -r <rot>
def brute_rot26(cipher):
for i in range(0, 26):
plain = ''
for c in cipher:
if c.isalpha():
if c.islower():
plain += chr((ord(c) - i - ord('a')) % 26 + ord('a'))
else:
plain += chr((ord(c) - i - ord('A')) % 26 + ord('A'))
else:
plain += c
print(f"ROT-{i}: {plain}\n")
return
def brute_rot47(cipher):
for i in range(0, 94):
plain = ''
for c in cipher:
if c.isprintable():
plain += chr((ord(c) - i - 33) % 94 + 33)
else:
plain += c
print(f"ROT-{i}: {plain}\n")
return
if __name__ == '__main__':
import argparse
parser = argparse.ArgumentParser(description='A simple python script to exploit the small keyspace of shift ciphers.')
parser.add_argument('-f', '--file', help='The cipher text to decrypt.', required=True, type=argparse.FileType('r'))
parser.add_argument('-r', '--rot', help='The ROT cipher to use.', default=26, type=int)
args = parser.parse_args()
file = args.file
cipher = file.read().strip()
if args.rot == 47:
brute_rot47(cipher)
else:
brute_rot26(cipher)
print('Done.')